Move or copy an SSL certificate from an Apache server to a Windows server
If you have multiple servers that need to use the same SSL certificate, such as in a load-balancer environment or using a wildcard or UC SSL certificates, you can convert the certificates and private key to a .pfx file and then import the certificate on Windows server so it can be used in IIS or Exchange. This may also be necessary when you switch hosting companies. We will be going over the exact process with step-by-step instructions in this article. If necessary, you can copy the SSL certificate from a Windows server to an Apache server instead.
We will assume that you have already successfully installed the SSL certificate on the Apache web server. You will follow these steps to move or copy that working certificate to the Windows server:
- Convert the individual certificate files and private key to a .pfx file.
- Copy the .pfx file to the Windows server.
- Import the .pfx file to the Windows store.
- Configure your IIS web sites to use the certificate.
Create the .pfx file using OpenSSL
The SSL certificate on your Apache server consists of a primary certificate, a private key, and probably one or more intermediate certificates. You will need to locate all of those files and convert them into a .pfx file using OpenSSL (instead of using OpenSSL, you can use the SSL Converter to convert the .pem/.crt files to a .pfx file).
- Find all the individual files on the Apache server. Their exact location will be specified in your Apache configuration file if they are currently being used. Make sure you have OpenSSL installed on the server.
-
Run this OpenSSL command to create a text file with the contents of the .pfx file:
openssl pkcs12 -export -out mydomain.pfx -inkey mydomain.key -in mydomain.crt -certfile intermediateCA.crtMake sure that mydoman.key is your private key file, mydomain.crt is your primary/server certificate for your domain name, and intermediateCA.crt is your intermediate certificate if you have one.
You can now copy that .pfx file to the Windows server and import it using the instructions below. The following screenshots are from a Windows Server 2008 machine but any differences for Windows Server 2003 are noted.
Import the certificate in the Windows MMC console
Note: These instructions will have you import the certificate using the MMC console. If you have Windows Server 2008 (IIS7) you can also import and export certificates directly in the Server Certificates section in IIS. Click here to hide or show the images
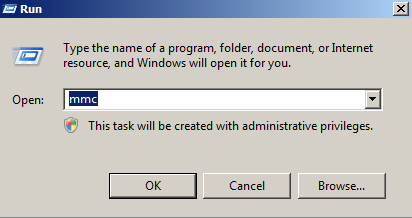
- Click on the Start menu and click Run.
- Type in mmc and click OK.
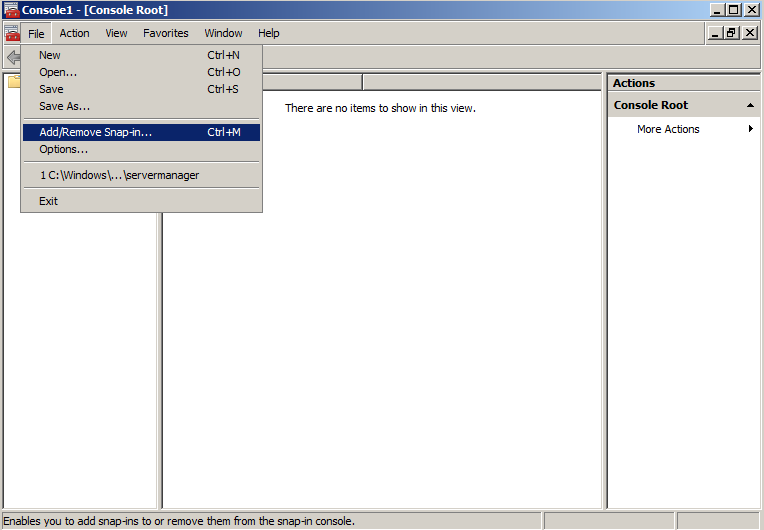
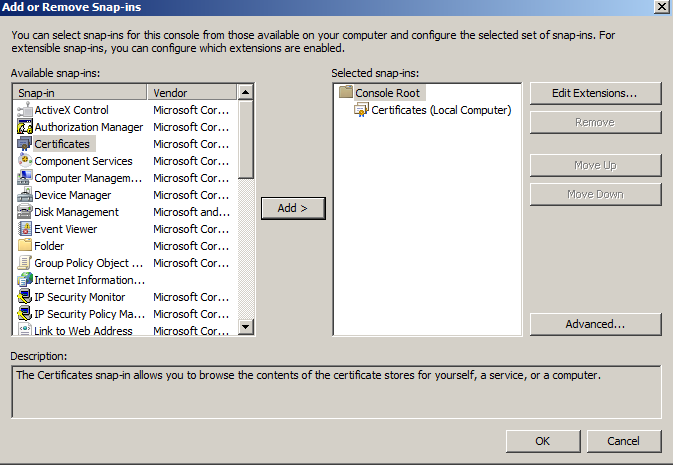
- Click on the File menu and click Add/Remove Snap-in...
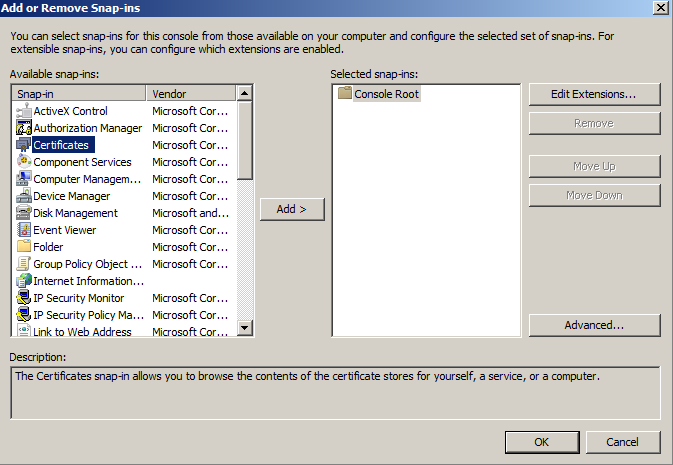
- If you are using Windows Server 2003, click on the Add button. Double-click on Certificates.
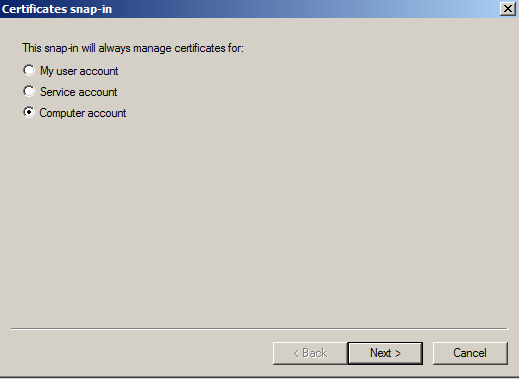
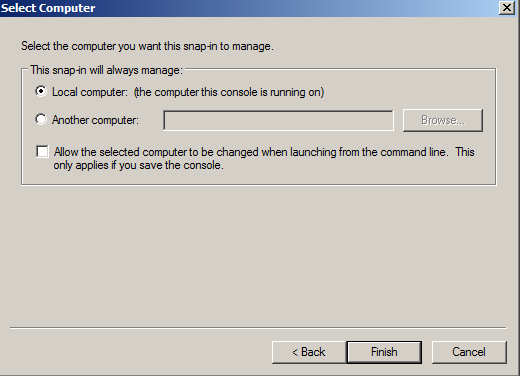
- Click on Computer Account and click Next.
- Leave Local Computer selected and click Finish.
- If you are using Windows Server 2003, click the Close button. Click OK.
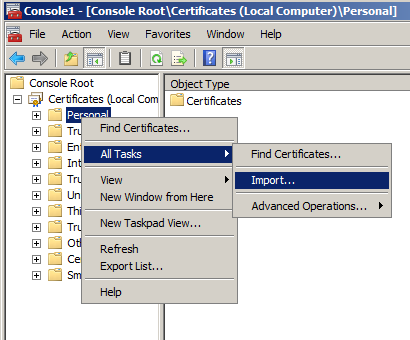
- Right-click on the Personal folder and select All Tasks and then Import...
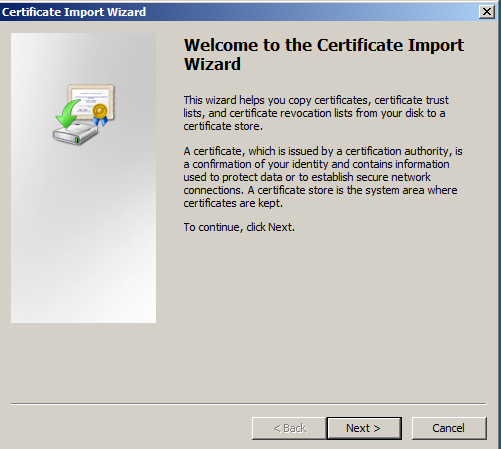
- In the Certificate Import Wizard click Next.
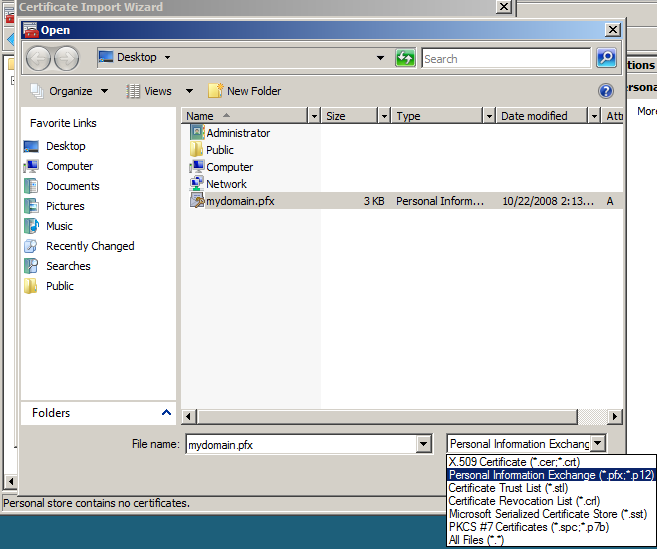
- Click the Browse button and change the file type from "X.509..." to "Personal Information Exchange (*.pfx, *.p12)". find the .pfx file that you copied over and click Open and then Next.
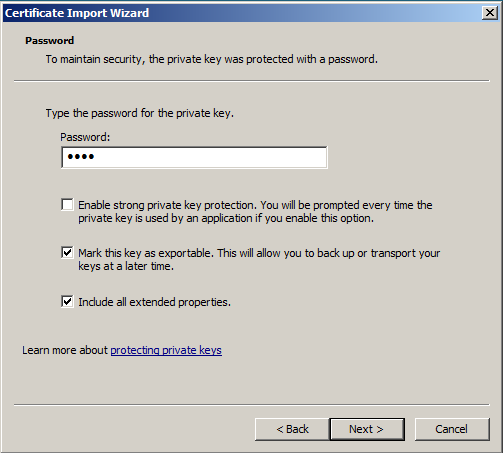
- Enter the password that you set when you exported the .pfx file and click "Mark this key as exportable" so you can export the certificate from this machine as well as the original. Click Next.
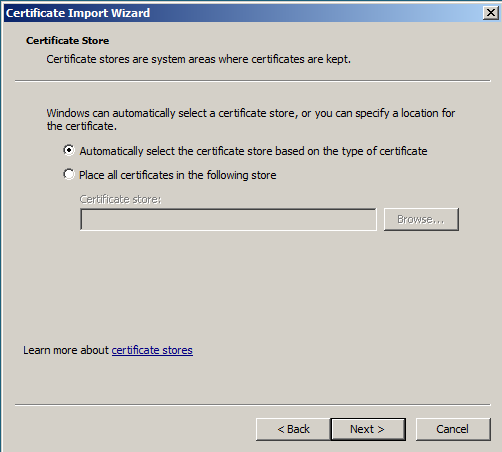
- Click "Automatically select the certificate store based on the type of certificate" and click Next.
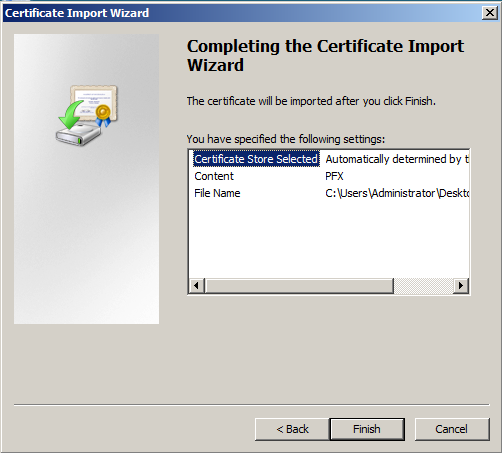
- Click Finish to complete the wizard.
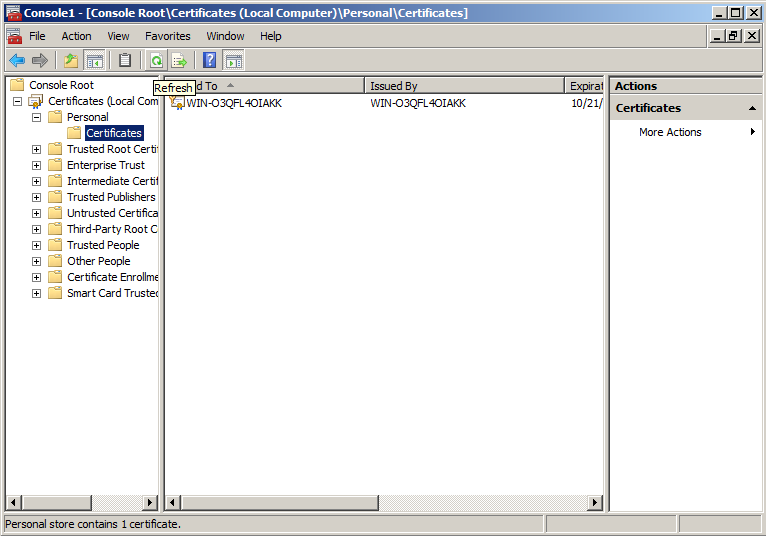
- You can now click the Refresh button in the toolbar to refresh and find your certificate in the Certificates folder under Personal. You can verify that it was imported correctly by double-clicking it and looking for "You have a private key that corresponds to this certificate" at the bottom of the certificate dialog.
- Close the MMC console. You do not need to save any changes.
Assigning the SSL certificate
After you have imported the .pfx file, you will either need to assign the certificate in IIS, enable the certificate for the services you need in Exchange or select the certificate in any other software that you are using. Because IIS is the most common place to use SSL certificates, we have included the instructions for assigning a website to use the new certificate in IIS 6 (Windows Server 2003). If you have Windows Server 2008, just follow the binding part of the IIS 7 SSL Certificate Installation instructions.
- In IIS, right-click on the website that needs the certificate and click on Properties.
- Click the Directory Security tab and click on the Server Certificate button to run the server certificate wizard.
- If you already have a certificate on that website you will need to remove it and then start the wizard again.
- Click "Assign an existing certificate" and click Next.
- Select the new certificate that you just imported and click Next.
- Click Finish. You may need to restart IIS for the certificate to start working with the assigned website.
While there are several steps in the process, moving an SSL certificate from an Apache server to a Windows server is quite simple. It involves creating a .pfx file from the individual certificates on the Apache server and importing it on the Windows server. If you need to move your SSL certificate to or from a different type of server, select the server type on our main SSL Certificate Import/Export Page
Originally posted on Sun Nov 9, 2008


Comments