How to Create a Self Signed Certificate using Java Keytool
 Securing your Java application with an SSL certificate can be extremely important. Fortunately, it is (usually) quite simple to do using Java Keytool. Most situations require that you buy a trusted certificate, but there are many cases when you can generate and use a self signed certificate for free.
Securing your Java application with an SSL certificate can be extremely important. Fortunately, it is (usually) quite simple to do using Java Keytool. Most situations require that you buy a trusted certificate, but there are many cases when you can generate and use a self signed certificate for free.
When to Use a Keytool Self Signed Certificate
An SSL certificate serves two essential purposes: distributing the public key and verifying the identity of the server so users know they aren't sending their information to the wrong server. It can only properly verify the identity of the server when it is signed by a trusted third party. A self signed certificate is a certificate that is signed by itself rather than a trusted authority. Since any attacker can create a self signed certificate and launch a man-in-the-middle attack, a user can't know whether they are sending their encrypted information to the server or an attacker. Because of this, you will almost never want to use a self signed certificate on a public Java server that requires anonymous visitors to connect to your site. However, self signed certificates have their place:
Never use a self signed certificate on an e-commerce site or any site that transfers valuable personal information like credit cards, social security numbers, etc.
- An Intranet. When clients only have to go through a local Intranet to get to the server, there is virtually no chance of a man-in-the-middle attack.
- A Java development server. There is no need to spend extra cash buying a trusted certificate when you are just developing or testing an application.
- Personal sites with few visitors. If you have a small personal site that transfers non-critical information, there is very little incentive for someone to attack the connection.
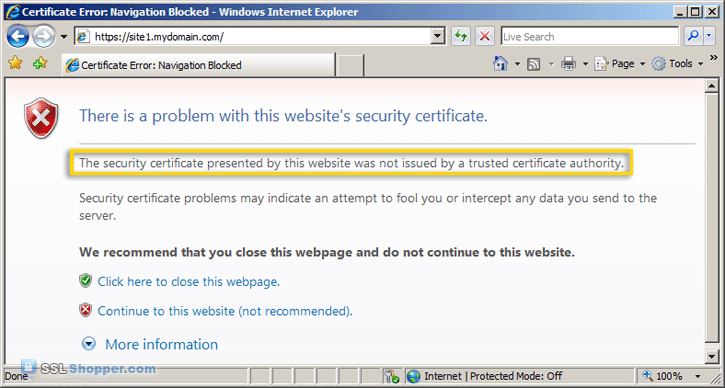
Just keep in mind that visitors will see a warning in their browsers (like the one below) when connecting to a server that uses a self signed certificate until it is permanently stored in their certificate store.
Generate a Self Signed Certificate using Java Keytool
Now that you know when to use a Keytool self signed certificate, let's create one using a simple Java Keytool command:
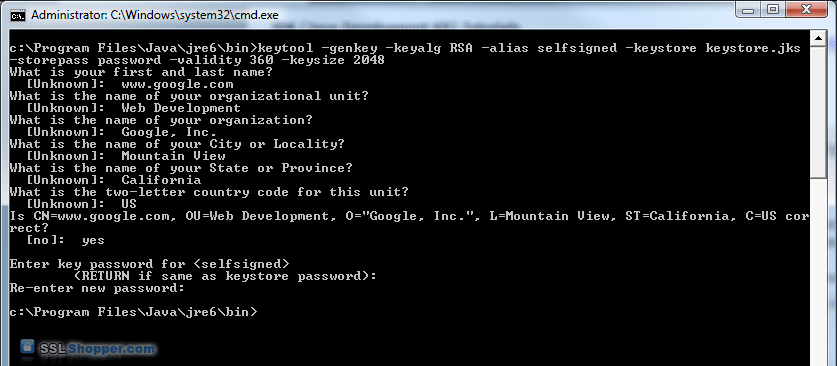
- Open the command console on whatever operating system you are using and navigate to the directory where keytool.exe is located (usually where the JRE is located, e.g. c:\Program Files\Java\jre6\bin on Windows machines).
- Run the following command (where validity is the number of days before the certificate will expire):
keytool -genkey -keyalg RSA -alias selfsigned -keystore keystore.jks -storepass password -validity 360 -keysize 2048 - Fill in the prompts for your organization information. When it asks for your first and last name, enter the domain name of the server that users will be entering to connect to your application (e.g. www.google.com)
This will create a keystore.jks file containing a private key and your sparklingly fresh self signed certificate. Now you just need to configure your Java application to use the .jks file. If you are using Tomcat, you can follow our Tomcat SSL Installation Instructions.
For more information on creating a Java Keytool Self Signed Certificate, see the following links:
Originally posted on Sat Oct 30, 2010


Comments